Since it usually operates in an open and shared environment, it is susceptible for data loss, theft, and malicious assaults. For instance, when healthcare suppliers use safe systems to communicate with sufferers about their well being, somewhat than transmitting well being knowledge via personal e-mail accounts, wiki.heycolleagues.com this type of data communication is an instance of a safe implementation. Beside the lack of requirements, regulations, and interoperability issues, the main obstacles that are hindering the wide-scale adoption of the cloud by healthcare suppliers are the safety, confidentiality, and trust points . It can provide quick, flexible, descubra como scalable, and cost-effective infrastructure and functions. In this paper, we examine the use of cloud computing in the healthcare trade and completely different cloud security and privacy challenges. The Quizlet flashcards, which WIRED discovered by way of basic Google searches, seem to incorporate delicate details about gate safety at Customs and Border Safety places. Customer conversations with chatbots can embrace contact data and personal details that make it easier for scammers to launch phishing assaults and commit fraud.
- Not each healthcare group has the in-house sources to manage the full complexity of securing cloud-based EHR methods and that’s not a weak point, it’s a actuality.
- District Courtroom case dominated that regulation enforcement can legally compel users to unlock their phones by way of such biometric knowledge .
- Not only is it a step closer to a digital NHS, the project reduces the motion of records between practices, freeing up area in practices which are used to store data as nicely as having the added benefit of being more environmentally pleasant
- If you are serious about making an attempt to create the locked filing cupboard on-line then you want to know about End-to-End Encryption, typically shortened to E2EE.
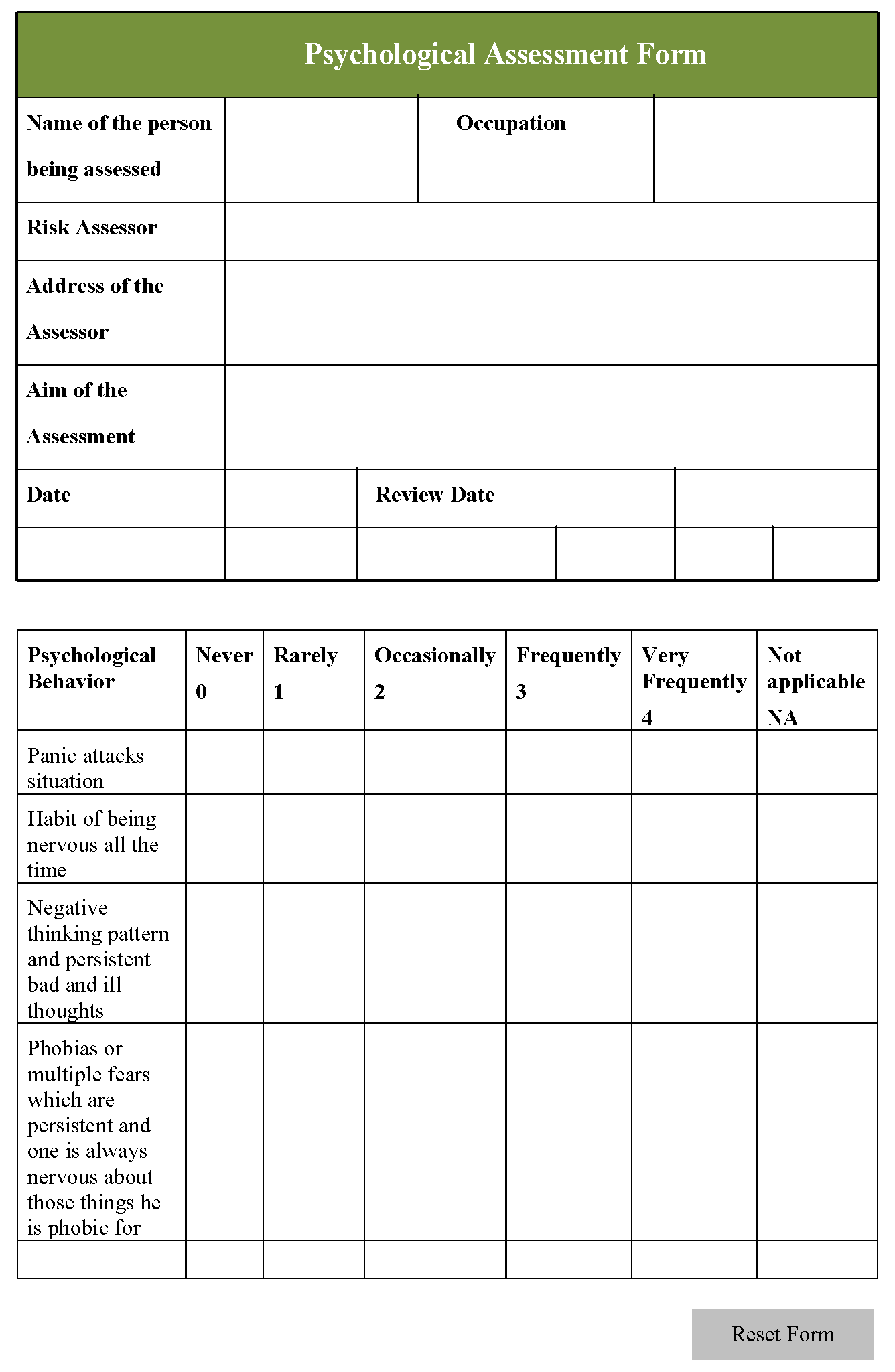
EHRs could embody a variety of data, including demographics, medical historical past, treatment and allergies, immunization standing, laboratory test results, radiology photographs, important signs, personal statistics like age and weight, and billing information. Compared with conventional on-premises data facilities, the cloud can supply numerous advantages for storing EHRs. As the quantity of these digital data continues to rise, more providers at the moment are contemplating storing them in the cloud. Still, attaining HITRUST certification could be a complicated, time-consuming course of. The MSP may help you select and configure cloud-based companies while enabling you to implement automated tools for ongoing compliance monitoring. Some CSPs will supply additional services or tools to help you adjust to rules.
Dropbox Enterprise: Greatest For Accessible Cloud Storage
Discover the Field App Center, and if your favourite apps aren’t listed, you ought to use Zapier to hyperlink Field with other well-liked functions.
 To study more about how I evaluated the most effective HIPAA-compliant cloud storage suppliers, please discuss with the methodology section on the finish of this article. Fit Small Business (FSB) is a trusted supply for expertise advice among small business house owners as a outcome of we adhere to a rigorous editorial policy that prioritizes goal and accurate content. Primarily Based on my skilled review of several HIPAA-approved cloud storage providers, here are the six high selections and their major use instances. When it comes to protecting sensitive info, selecting the best HIPAA-compliant cloud storage supplier can make a big difference. Fit Small Enterprise provides unbiased, editorially unbiased content material and evaluations.
To study more about how I evaluated the most effective HIPAA-compliant cloud storage suppliers, please discuss with the methodology section on the finish of this article. Fit Small Business (FSB) is a trusted supply for expertise advice among small business house owners as a outcome of we adhere to a rigorous editorial policy that prioritizes goal and accurate content. Primarily Based on my skilled review of several HIPAA-approved cloud storage providers, here are the six high selections and their major use instances. When it comes to protecting sensitive info, selecting the best HIPAA-compliant cloud storage supplier can make a big difference. Fit Small Enterprise provides unbiased, editorially unbiased content material and evaluations.Learn Extra About Note Taking
More info This is the URL your shared files shall be out there for download Data backup is crucial in HIPAA-compliant cloud storage as dropping patient knowledge isn't an choice. With HIPAA-compliant cloud storage, healthcare organizations can securely retailer, share, and entry delicate patient data whereas maintaining compliance with strict privateness laws, making certain each safety and efficiency in their operations. It offers a secure and scalable solution for storing delicate medical data, ensuring confidentiality, integrity and availability. HIPAA-compliant cloud storage is important for organizations that handle Protected Health Info (PHI) to make sure compliance with the Medical Insurance Portability and Accountability Act (HIPAA). FileCloud ensures HIPAA compliance via several secure options and insurance policies like information encryption (both in transit and at rest), audit trails, safety insurance policies and controls, restricted employee access to customer data information and far more. Jotform is your on-line varieties answer that permits HIPAA compliance
Physical Information Storage
- They can see that you're storing an encrypted file, but they've completely no method of knowing what's inside it.
- It stores data corresponding to information, movies, or images on distant servers managed by third-party providers and may be accessed by way of the internet.
- Defending clinical notes isn’t just a compliance task—it’s a half of sustaining a powerful, respectful relationship with the people you're employed with.
Edge computing goals at processing knowledge on the fringe of the community somewhat than processing data on the data center as in traditional eHealth cloud solutions. Encrypting of information in transit is the method of encrypting data at one location, transferring it over the community, then decoding data on the cloud. Since patient PHR saved within the cloud or at third get together, there have been broad privateness issues as a end result of affected person private well being information could be used by third-party servers or unauthorized customers. Each applications implement a centralized structure the place sufferers store and apobangpo.wiki replace health data in EHR system, and sufferers have full management over their information . Part thirteen in Determine three includes controls on community security management and data switch. For occasion, identities of the sufferers could be made nameless after they retailer their well being data on the cloud in order that the cloud servers could not be taught about the identification.
Designed By Clinicians - For Healthcare And Allied Health Professionals
With escalating threats, legal dangers, and public belief at stake, hipaa compliant cloud storage is your first line of protection. By leveraging NoteNest’s tools and following finest practices, therapists can ensure their notes stay secure, organized, and fully compliant with HIPAA laws. Azure offers a complete set of tools and providers for storing, processing, and analyzing healthcare data securely. To enhance the belief on this relatively new know-how, cloud computing applications have a quantity of safety requirements to be fulfilled. Be Taught finest practices, legal tips, and tech safeguards from Twofold’s specialists. An perfect therapy notes software program integrates properly with EHRs, accounting platforms, telehealth techniques, and scheduling tools—reducing the want to juggle a number of functions. The entire work course of is re-imagined from the ground up in close collaboration with psychologists, psychotherapists and counsellors.
Company-wide government evaluate A Cloud firm should be periodically audited and supported by an inner audit group. In case of failure of certainly one of these data facilities, automated processes transfer the shopper data traffic away from the affected space. Before updating software, these updates should be reviewed, experimented, and approved. The software updating course of ought to be designed to avoid unintended service disruptions and maintain the integrity of service to the customer. Climate and temperature In order to prevent overheating of the servers, climate control is required. Account review Each access account is reviewed in Cloud platforms each 90 days.
"the Cloud Isn't As Safe As On-premises Environments"
NoteNest permits therapists to customize privacy settings, such as information retention durations, restricted entry for certain notes, and automatic compliance checks. Therapists utilizing NoteNest receive compliance training assets and buyer assist to ensure they comply with finest practices. If therapists need to share notes or focus on sensitive information with shoppers, NoteNest supplies secure messaging and document-sharing features. This session timeout function reduces the risk of unauthorized information exposure in shared or public workspaces.
 HIPAA mandates that therapists keep an audit trail of who accesses or modifies therapy notes. NoteNest offers automated and encrypted backups, guaranteeing that therapists can recuperate knowledge shortly in case of sudden issues. This feature helps preserve privateness and ensures compliance with HIPAA’s minimal essential rule.
HIPAA mandates that therapists keep an audit trail of who accesses or modifies therapy notes. NoteNest offers automated and encrypted backups, guaranteeing that therapists can recuperate knowledge shortly in case of sudden issues. This feature helps preserve privateness and ensures compliance with HIPAA’s minimal essential rule.Tips On How To Support Hipaa Compliance With Filecloud Cloud Storage
Nonetheless, synchronization applications for distributed storage fashions are solely useful as soon as report standardization has occurred. Once More, overall requirements for the design and security of the system and its archive will vary and must perform beneath ethical and authorized ideas particular to the time and place.[citation needed] These entities include, however are not restricted to, major care physicians, hospitals, insurance coverage corporations, and sufferers. Personal health information is efficacious to individuals and it is subsequently tough to assess whether a breach will cause reputational or financial hurt or adversely affect one's privacy. These safeguards add safety for data which would possibly be shared electronically and give patients some essential rights to observe their medical information and receive notification for loss and unauthorized acquisition of well being information. The implementation of the Cross-Border Health Directive and the European Fee's plans to centralize all health information are of prime concern to the EU public who believe that the well being care organizations and governments can't be trusted to manage their information electronically and expose them to extra threats.
Philosophical Views
For example, the fog and bbarlock.com edge computing applied sciences rely on distributed knowledge processing across many locations somewhat than inside a small and restricted number of places in case of cloud storage and conventional knowledge facilities. Fog computing goals to process knowledge as close as the service invoker (e.g., IoT wearable health devices), which may help scale back unnecessary latency in eHealth providers. Finally, with the rising demand for better performance and scalability of eHealth systems and the wide adoption of IoT (Internet of things), emerging applied sciences such as edge and fog computing are used to enhance cloud computing. In cloud computing, delicate data-in-rest suffers many threats that can cause information leakage.
Offering patients access to their health data, together with medical histories and take a look at outcomes by way of an EHR, is a legal right in some parts of the world. It has been reported that these errors have been reduced by "55-83%" because records are actually on-line and require particular steps to keep away from these errors. This is acknowledged by the elevated security necessities for electronic medical data included within the Medical Insurance Portability and Accountability Act (HIPAA) and by large-scale breaches in confidential information reported by EMR users. An EMR consists of the medical and therapy historical past of patients treated by that particular practice. EMRs are essentially digital variations of the paper documents used in a clinician's office, usually functioning as an inside system within a practice.







